Keep up to date on current trends and technologies
Ruby

A Comparison of Ruby Version Managers for macOS
Daniel Kehoe

RubyMine: Code Insight for Ruby and Rails
Artem Sarkisov

Understanding the Model-View-Controller (MVC) Architecture in Rails
Glenn Goodrich

Building APIs with Ruby on Rails and GraphQL
Léonard Hetsch

Beyond Rails Abstractions: A Dive into Database Internals
David Bush

Search and Autocomplete in Rails Apps
Ilya Bodrov-Krukowski

Start Your SEO Right with Sitemaps on Rails
Ilya Bodrov-Krukowski

Handle Password and Email Changes in Your Rails API
Vinoth
Do the Right Thing and Document Your Rails API with Swagger
Parth Modi

Master Many-to-Many Associations with ActiveRecord
Fred Heath

Setting Up an Angular SPA on Rails with Devise and Bootstrap
Jesse Novotny
Lexers, Parsers, and ASTs, OH MY!: How Ruby Executes
David Bush

Common Rails Security Pitfalls and Their Solutions
Ilya Bodrov-Krukowski

Ruby, Rails, and Imposter Syndrome, with Glenn Goodrich
M. David GreenTim Evko
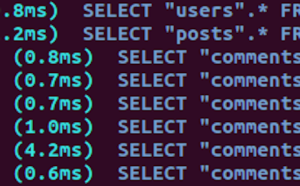
N + 1: When More Queries Is a Good Thing
Parth Modi

Video Uploads with Rails and Ziggeo
Ilya Bodrov-Krukowski

Leverage Heroku’s Metrics for Better App Performance
Vinoth

Rack-App: A Performant and Pragmatic Web Microframework
David Bush

From Novice to Ninja: How to Master Using Plugins in Rails
Glenn Goodrich

7 Design Patterns to Refactor MVC Components in Rails
Viktoria Kotsurenko

Real-Time Messaging with Rails and ActionCable
Ilya Bodrov-Krukowski

The Basics of MVC in Rails: Skinny Everything
Viktoria Kotsurenko

Build a Messaging System with Rails and ActionCable
Ilya Bodrov-Krukowski

10 Ruby on Rails Best Practices
Sarmad Sabih

Password-Less Authentication in Rails
Vinoth

Learn Ruby Metaprogramming for Great Good
Ilya Bodrov-Krukowski

DRY Off Your Rails Code with ActiveSupport::Concerns
Kingsley Silas
Diving into How Hashes Work in Ruby
David Bush
Quick Tip: Use Enums in Rails for Mapped Values
William Kennedy

Authenticate Your Rails API with JWT from Scratch
Vinoth

Create a Twitter GUI Client with Shoes
Ardian Haxha

Rails: Dynamically Chain Scopes to Clean up SQL Queries
William Kennedy
Showing 32 of 419