How to Add OAuth Authentication to Your Twitter App
Thanks Twitter. Not only have you removed open access to public Twitter timelines, you’re expecting developers to contend with cryptic authentication documentation!
Many of us simply want to display our own tweets on our own website, but it’s obvious Twitter prefers us to use their widgets. Despite the convoluted Twitter instructions, implementing OAuth in your lovingly-crafted API 1.0 application is reasonably straight-forward if you use the libraries provided by talented group of (non-Twitter) developers .
In the example below, we’re going to apply Twitter OAuth authentication to a PHP application which previously parsed timeline data from a REST URL such as:
https://api.twitter.com/1/statuses/user_timeline.json?screen_name=craigbuckler
There are also Twitter libraries for C, Clojure, .NET, Go, Java, Node.js, Lua, Objective-C, Perl, Python and Ruby — the instructions will be similar.
Step 1: Create Your Twitter Application
Head to dev.twitter.com/apps/ and log in using your Twitter ID and password. This can be any account; your application will be able to read any other user’s timeline without their knowledge or permission (I realize that doesn’t make much sense given Twitter’s new policies, but I didn’t make the rules!)
Click the Create a new application button and enter the name and description of your application. The website should be a page where you can download your code but, since you’re still writing it, enter your home page URL and change it later. Leave the callback URL blank.
Complete the CAPTCHA and click Create.
Step 2: Create an Access Token
Click the Create my access token button at the bottom of the Details tab on your application’s page. You’ll now see various strings against:
- OAuth: Consumer key
- OAuth: Consumer secret
- Token: Access token
- Token: Access token secret
Keep the page open — you’ll need these shortly.
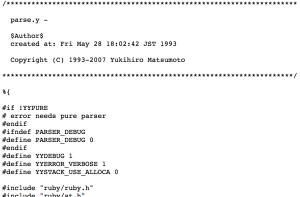
Step 3: Download the OAuth Library
Download Abraham Williams’ PHP Twitter OAuth library from github.com/abraham/twitteroauth.
The project contains a number of files, but the only ones you actually require are OAuth.php and twitteroauth.php in the twitteroauth folder. Copy both to a suitable folder in your application.
Step 4: Modify Your Timeline Fetching Code
Your PHP should now use code such as this to fetch a user’s timeline:
require('twitteroauth.php'); // path to twitteroauth library
$consumerkey = '11111111';
$consumersecret = '22222222';
$accesstoken = '33333333';
$accesstokensecret = '44444444';
$twitter = new TwitterOAuth($consumerkey, $consumersecret, $accesstoken, $accesstokensecret);
$tweets = $twitter->get('https://api.twitter.com/1.1/statuses/user_timeline.json?screen_name=craigbuckler&count=10');
print_r($tweets);
The variables $consumerkey, $consumersecret, $accesstoken and $accesstokensecret must be set to the Twitter codes generated in Step 2 above.
The $twitter->get method must then be passed an appropriate REST URL. The example shows mine so you should enter your own Twitter ID for the screen_name parameter (unless you specifically want to display my tweets moaning about Twitter?)
Run the code and, with luck, a stream of tweets should appear … in exactly the same way they did before the Twitter police insisted on restricting access to public messages. You’ll now need to format them according to the display requirements. Shesshh.
Note that TwitterOAuth’s get() method runs PHP’s json_decode command and returns an object. If you’d prefer an associative array, change line 144 of twitteroauth.php to:
return json_decode($response, true);Hopefully, that should provide a few months grace until Twitter force us to migrate to API 2.0 and jump through more flaming hoops. Best of luck.
Frequently Asked Questions about Twitter 1.1 OAuth with PHP
What is Twitter 1.1 OAuth with PHP?
Twitter 1.1 OAuth with PHP is a method of authentication that allows a user’s application to interact with the Twitter API. It uses the OAuth 1.1 protocol, which is a secure and user-friendly way to authorize applications to access Twitter data without sharing passwords. PHP, a popular server-side scripting language, is used to implement this authentication process.
How does Twitter 1.1 OAuth with PHP work?
Twitter 1.1 OAuth with PHP works by exchanging a set of keys and tokens between the user’s application and Twitter. The application sends a request to Twitter with its consumer key and secret. Twitter then returns a request token. The user is redirected to Twitter to authorize the application, and upon successful authorization, Twitter sends back an access token and secret. The application can then use these to access Twitter data.
How do I get started with Twitter 1.1 OAuth with PHP?
To get started with Twitter 1.1 OAuth with PHP, you first need to create a Twitter application on the Twitter Developer site. Once you have your application, you can obtain your consumer key and secret. You then need to install the TwitterOAuth PHP library, which provides functions to interact with the Twitter API. You can then use this library to implement the OAuth process.
What are the benefits of using Twitter 1.1 OAuth with PHP?
Using Twitter 1.1 OAuth with PHP has several benefits. It provides a secure way to access Twitter data without sharing passwords. It also allows for more granular control over what data the application can access. Additionally, using PHP makes it easy to implement the OAuth process, as there are many libraries and resources available.
Can I use Twitter 1.1 OAuth with other programming languages?
Yes, while this guide focuses on PHP, Twitter’s OAuth 1.1 protocol can be used with any programming language that can make HTTP requests and handle responses. There are libraries available for many languages, including Python, Ruby, and Java.
What is the difference between OAuth 1.0 and OAuth 1.1?
OAuth 1.1 is an updated version of OAuth 1.0. It includes several improvements, such as better handling of non-ASCII characters and more detailed error messages. However, the basic process of exchanging keys and tokens remains the same.
What data can I access with Twitter 1.1 OAuth?
With Twitter 1.1 OAuth, you can access a wide range of data, including tweets, user profiles, and follower lists. The exact data you can access depends on the permissions granted to your application by the user.
How do I handle errors in Twitter 1.1 OAuth with PHP?
When using Twitter 1.1 OAuth with PHP, errors can be handled using the standard PHP error handling mechanisms. Additionally, the Twitter API will return error messages in the response if there is a problem with the request.
Is Twitter 1.1 OAuth with PHP secure?
Yes, Twitter 1.1 OAuth with PHP is secure. It uses the OAuth protocol, which is designed to provide secure authorization without sharing passwords. Additionally, all communication with the Twitter API is done over HTTPS, ensuring that the data is encrypted.
Can I use Twitter 1.1 OAuth with PHP for commercial applications?
Yes, you can use Twitter 1.1 OAuth with PHP for commercial applications. However, you must comply with Twitter’s Developer Agreement and Policy, which includes rules about how you can use and display Twitter data.
Craig is a freelance UK web consultant who built his first page for IE2.0 in 1995. Since that time he's been advocating standards, accessibility, and best-practice HTML5 techniques. He's created enterprise specifications, websites and online applications for companies and organisations including the UK Parliament, the European Parliament, the Department of Energy & Climate Change, Microsoft, and more. He's written more than 1,000 articles for SitePoint and you can find him @craigbuckler.
Published in
·Animation·Animation·CSS·Design·Design & UX·HTML & CSS·Illustration·JavaScript·Tools & Libraries·July 18, 2014