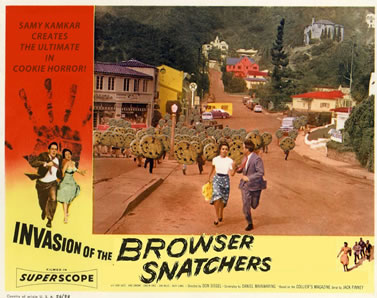
Over the past year or so there’s been a slowly building hubbub as the general news media became aware of Flash cookies and their ability to tag and identify return visitors — even after those users have actively cleared their HTTP cookie cache.
And they thought they had some trouble then?
Developer Samy Kamkar has just released a new JavaScript API called Evercookie that employs ten — yes, count ‘em — ten different methods for virtual-tattooing a cookie into your browser.
Some of Evercookie’s tagging methods are so fiendishly clever that you can only imagine that Samy codes them from deep inside a secret volcano lair, complete with henchmen and a shark pool. Currently Evercookie uses:
- Standard HTTP Cookies
- Local Shared Objects (Flash Cookies)
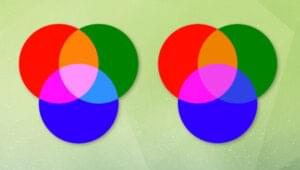
- Storing cookies in RGB values of auto-generated, force-cached PNGs
- Reading cookies into and out of Web History
- Storing cookies in HTTP ETags
- Internet Explorer userData storage
- HTML5 Session Storage
- HTML5 Local Storage
- HTML5 Global Storage
- HTML5 Database Storage via SQLite
But it is time for Samy to rest on his laurels? Oh no sir! Plans are already in the pipeline for a version that tags users using Silverlight, Java and window.name.
What’s more, any time Evercookie discovers any of it’s cookies missing, it quietly and efficiently recreates and replaces them. And people say you can’t get good help these days.
While some of the methods Samy employs are well documented (i.e. HTTP cookies, Flash cookies), many are original ideas to my knowledge.
For instance, the force-cached PNG method is almost like a surreptitious DIY QR code system. The user’s unique ID is converted into a series of colored pixels in PNG and then forcibly cached. When the user returns, the PNG is loaded quietly into a canvas element where the ID is extracted.
The Web History cookie method is possibly even more insidious. A temporary page is created in the background with the URL of your unique ID — let’s say ‘pwn.com/yourusernameABC-‘. This page is sent to your browser alone and recorded in your browser history.
The next time you return your browser rifles through URL variations and compares each one to your web history. When a partial match is found (i.e.'pwn.com/y‘) it locks that in and moves to the next letter — a little like the way autocomplete works on your address bar. Whenever it gets to a hyphen it knows it has a complete ID.
HTML5 also seems to have opened up a host of cosy new nooks for cookies to settle into. Yay for tech progress!
The interesting thing is the whole project is free and open source, so Samy seems to be taking a whitehat hacker approach of publicizing a vulnerability to allow people to counter it. Right now, the only known counter to Evercookie is Safari in private browsing mode.
Now I don’t know about you, but I can’t quite decide between a ‘Golly-gee-that’s-clever-Batman-geek-out ‘ and a hyper-ventilating, spluttering panic attack.
How about you?
 Alex Walker
Alex WalkerAlex has been doing cruel and unusual things to CSS since 2001. He is the lead front-end design and dev for SitePoint and one-time SitePoint's Design and UX editor with over 150+ newsletter written. Co-author of The Principles of Beautiful Web Design. Now Alex is involved in the planning, development, production, and marketing of a huge range of printed and online products and references. He has designed over 60+ of SitePoint's book covers.